The DOE allocated $160 million to energy sector cybersecurity in 2026 — not because the problem is getting easier, but because the threat has escalated in ways that were not the norm even three years ago. Dragos’s 2026 analysis describes adversaries who have moved beyond access and persistence into deliberate, active preparation for operational impact. The ‘Energy Threat Analysis Center Act of 2026,’ introduced this spring, reflects congressional recognition that the threat has escalated beyond what current information-sharing structures adequately address. Meanwhile, manufacturing ranked second in frequency of ransomware attack in the United States in the first two months of 2026, with 53 active threat groups claiming victims.
The underlying driver is the convergence of information technology and operational technology — and the uncomfortable reality that most operational security programs have not kept pace with how fast that convergence is happening. Distributed Energy Resource management platforms require real-time grid connectivity. Battery Energy Storage Systems require cloud-based management interfaces. Industrial IoT sensors connect previously isolated environments to broader networks. AI-based grid optimization requires data flows between systems that historically did not communicate. Each of these advances creates genuine operational value. Each also expands the attack surface in ways that legacy OT security architectures were not built to address.
Why Standard IT Security Frameworks Fail in OT Environments
IT cybersecurity frameworks were built for IT environments. They assume that availability is important but that confidentiality and integrity are often the primary concerns. They assume systems can be patched on reasonable timescales. They assume taking a system offline for maintenance is an operational inconvenience, not a safety or reliability event. None of those assumptions hold in
operational technology environments.
Availability is frequently the primary concern in OT. A generating unit taken offline because of a security patch window has immediate, quantifiable financial consequences — and depending on grid conditions, possible reliability implications. Industrial control systems in manufacturing run on proprietary protocols that standard IT security tooling does not speak. Safety systems in energy and industrial environments have isolation requirements that cannot be compromised for monitoring convenience. Effective OT security requires people who understand this from operational experience — not IT security specialists who have learned some OT vocabulary.
The SANS 2026 OT/ICS Cybersecurity report flagged a structural workforce skills crisis: 27 percent of organizations experienced breaches directly attributable to workforce skills gaps. This is where
CMMI-certified process discipline and purpose-built OT expertise become essential — not optional.
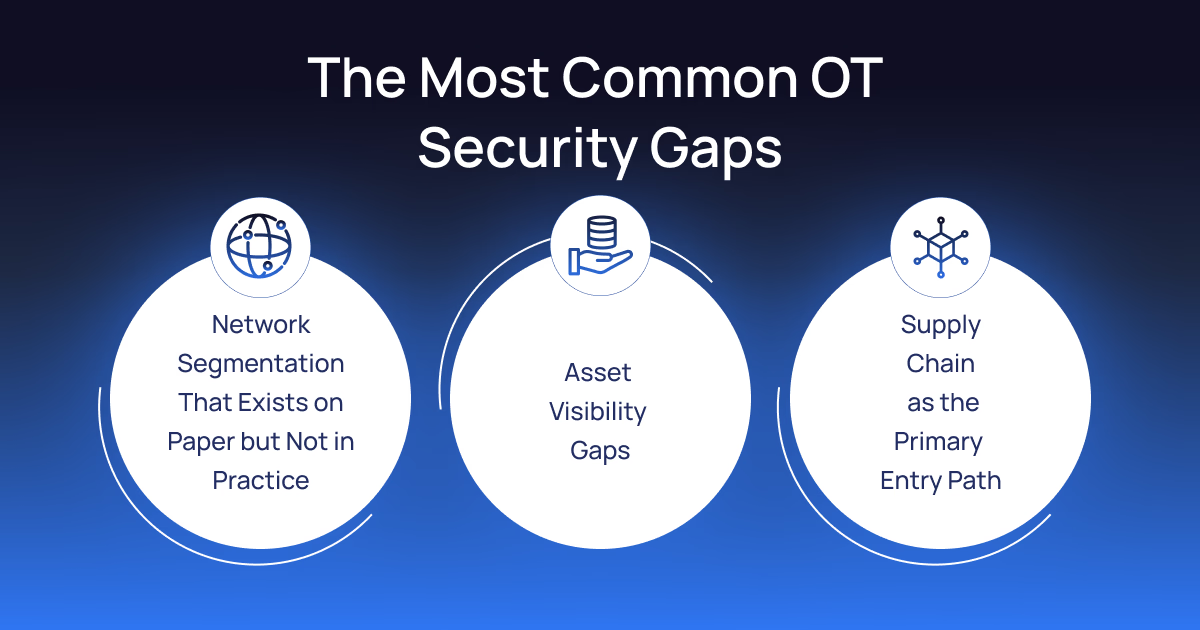
The Most Common OT Security Gaps — and Their Real Consequences
Network Segmentation That Exists on Paper but Not in Practice
Many energy operators and manufacturers have segmentation policies that look solid in the network diagram and have informal workarounds in production environments that undermine them entirely. An engineer who needs direct access to a historian for a maintenance task creates a connection that bypasses the segment boundary. A vendor who needs remote access to a control system gets credentials that allow far broader access than the specific function requires. Over time, the actual segmentation of the production environment diverges significantly from the documented architecture. The gap is not visible until an attacker exploits it.
Asset Visibility Gaps
You cannot protect what you cannot see. Most utilities and manufacturers have surprisingly poor OT asset visibility — particularly as IT/OT convergence has blurred the boundaries of what belongs in which inventory. This is why comprehensive
data foundations and asset governance are a prerequisite for any security architecture. Asset discovery in OT environments almost always produces surprises
Supply Chain as the Primary Entry Path
The most common entry path to operational technology networks now runs through vendors and integrators with legitimate remote access. Authentication platforms, managed service providers, and SaaS applications have become priority attack targets precisely because successful compromise provides simultaneous access to multiple downstream clients. Third-party access governance in OT environments — where vendor connections are often permanent and broadly scoped because operational continuity requirements make temporary, narrowly-scoped access difficult to manage — is not a solved problem at most operators.
How PiTech's OT Security Practice Helps Energy and Manufacturing Organizations
PiTech’s OT/ICS Cybersecurity practicewas developed for the specific security requirements of operational environments — not adapted from IT security frameworks. Our team has worked in both domains, understands the threat models specific to industrial environments, and builds security programs that work with operations rather than against it.
Our OT Asset Discovery and Inventory engagements produce comprehensive, verified asset inventories. We design and implement Network Architecture and Segmentation based on IEC 62443 zone-and-conduit models. For security monitoring, we deploy, tune, and operate Dragos, Claroty, and Nozomi — the purpose-built OT monitoring platforms that speak the industrial protocols standard IT tooling does not. Our NERC CIP Compliance service covers gap assessments, compliance program development, and ongoing compliance support.
PiTech holds CMMI certification, ISO 27001 certification, and ISO 9001 certification. Our process-first delivery model means security programs are documented, measured, and consistently applied — the discipline that OT security requires.
What Mature OT Security Architecture Looks Like
The energy and
manufacturing organizations managing OT security most effectively have made a deliberate choice to treat it as a first-class engineering discipline — dedicated OT security staff, purpose-built tooling, vendor security evaluation built into procurement processes, and incident response plans developed in coordination with operations leadership. Federal investment and legislative activity are signals about what is at stake. The actual security work happens at the operator level, and it requires both the technical expertise and the operational understanding to build programs that protect what actually needs to be protected.
Frequently Asked Questions (FAQs)