Table of Contents
Summarize and analyze this article with
Breach frequency in healthcare jumped more than 100 percent in the last year. As of current reporting, 39 separate provider incidents have been documented this year alone, affecting anywhere from hundreds to half a million individuals per event. The University of Mississippi Medical Center closed clinics entirely following a ransomware attack. BridgePay, serving municipalities and healthcare organizations, went dark for days. These are not edge cases. They are the new normal in a threat environment where healthcare combines high operational pressure with extremely sensitive data — the combination that sophisticated ransomware groups specifically optimize for.
At the same time, HHS finalized the most significant HIPAA Security Rule overhaul in years. Every previously addressable safeguard is now mandatory. Annual compliance audits are required. Technology asset inventories — AI tools included — are required. And OCR has made clear that enforcement will follow. If your security program was designed to pass a periodic audit in a calmer threat environment, it requires a fundamental rethink.
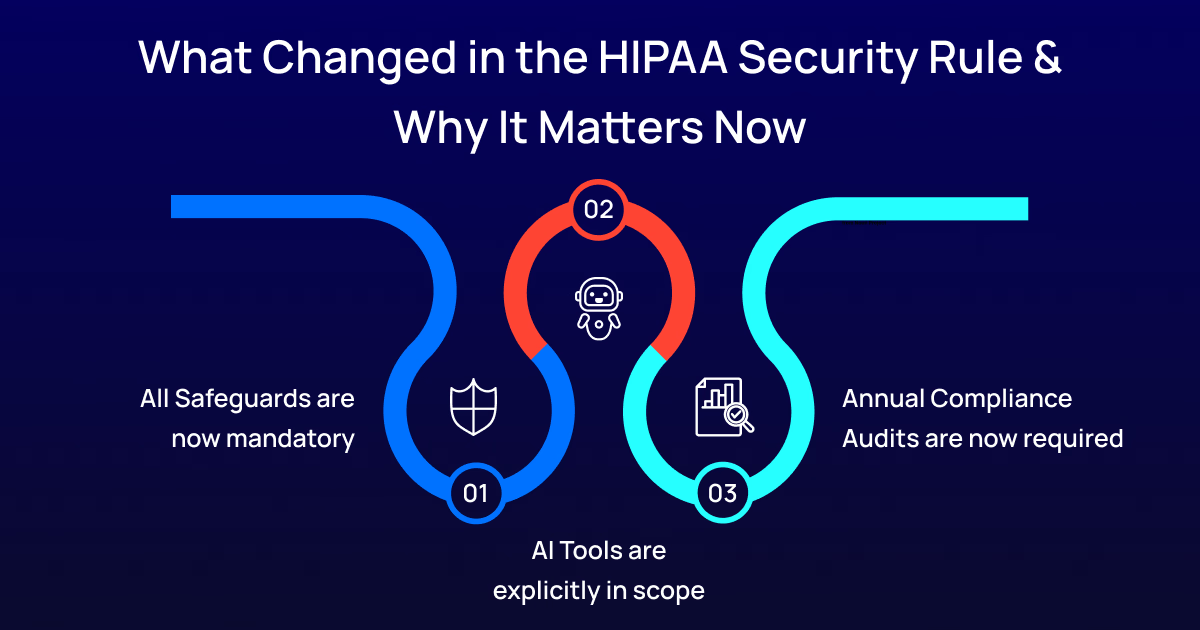
All Safeguards Are Now Mandatory
AI Tools Are Explicitly In Scope
Annual Compliance Audits Are Now Required
Shadow AI: The Threat Vector Healthcare Is Underestimating
Fortified Health Security’s 2026 Horizon Report specifically flags Shadow AI as an emerging insider threat in healthcare. Sixty-six percent of physicians use AI tools. Only 23 percent of health systems have Business Associate Agreements covering those tools. Every unsanctioned AI interaction with patient data is a potential HIPAA violation and a potential breach vector. Deepfakes and AI-powered social engineering attacks are also emerging as serious credential-compromise vectors, targeting healthcare’s complex vendor ecosystems and distributed workforces.
Addressing Shadow AI requires more than a policy memo. It requires knowing what is actually deployed across the organization — not just what IT approved. It requires technical controls that detect unauthorized data flows. It requires training that explains the reasoning behind governance requirements. And critically, it requires a governance process that operates faster than the workaround. If formal approval takes six months and a clinician needs help today, they will find a tool outside your control. Governance needs to be faster than the shadow.
How PiTech Helps Healthcare Organizations Build Security That Meets the New Reality
PiTech’s Healthcare Cybersecurity practice applies government-grade security standards — the same rigor used in federal health agency and defense health system engagements — to commercial healthcare clients. We do not offer generic IT security adapted for healthcare. We build security programs designed from the ground up for the specific threat profile and operational constraints of clinical environments.
Our healthcare cybersecurity engagements start with a comprehensive security posture assessment benchmarked against the updated HIPAA Security Rule requirements — mapping where you are today against every mandatory safeguard, with gap identification prioritized by regulatory risk and breach exposure. Our Shadow AI Discovery service identifies every AI tool in organizational use through network analysis, staff surveys, and vendor record review, producing a prioritized inventory that feeds directly into both our BAA Remediation service and our technical control implementation.
We implement Mandatory MFA across all systems touching ePHI — including legacy clinical applications, API connections, and service accounts that standard MFA deployments typically miss. We design and deploy End-to-End Encryption for ePHI at rest, in transit, and during processing, covering the intermediate stages where data flows between clinical systems, analytics platforms, and AI tools. Our Continuous Risk Analysis capability replaces periodic assessments with ongoing monitoring that integrates threat intelligence, vulnerability scanning, and incident data into regular risk reporting — producing the audit-ready evidence the updated rule requires.
For incident response, we build and test OT-specific plans with the documentation standards needed to satisfy CIRCIA’s 72-hour reporting requirements and HIPAA breach notification obligations simultaneously. Organizations that face an incident and need to satisfy both reporting regimes at speed require incident response architecture that was designed for that requirement, not adapted from a single-framework plan during the crisis.
PiTech’s ISO 27001 certified information security management and CMMI-certified delivery processes are what make our healthcare security programs auditable, repeatable, and sustainable. When OCR auditors ask how you validated that your AI systems do not expose PHI, you need an answer backed by documented procedures and evidence. We build the documentation as a natural byproduct of how we work, not as a separate compliance exercise after delivery.
Where Healthcare Organizations Should Focus Right Now
The five-step remediation priority: start with a Shadow AI inventory this week — identify every tool in use, not just what IT approved. Build a mandatory MFA roadmap immediately — map every system touching ePHI and identify which support modern authentication. Conduct an encryption gap analysis — document where ePHI is encrypted at rest and in transit and where it is not. Shift from annual to continuous risk analysis. And treat AI vendor management as a compliance function, not a procurement activity.
Security is not a project with a finish line in healthcare. It is a permanent operational discipline. The organizations that will handle the convergence of rising breach rates, updated HIPAA requirements, and expanding AI adoption will be the ones that have built that discipline into their operations — not the ones that respond to each new development as a separate crisis.




