Table of Contents
Summarize and analyze this article with
Introduction
In the Department of Defense (DoD), data warehousing and data architecture play a crucial role in managing and analyzing large amounts of information. These components work hand-in-hand to ensure efficient data storage, retrieval, and analysis within the department. Modern DoD data solutions encompass data warehousing, advanced data architecture, and integrated analytics platforms designed specifically for defense operations and national security requirements.
The foundation of effective defense data management rests on three critical pillars: centralized data repositories, robust security frameworks, and a scalable architecture that supports real-time intelligence and decision-making capabilities.
These components work synergistically to ensure that commanders, warfighters, and decision-makers have immediate access to accurate, actionable intelligence when mission-critical situations demand it.
Understanding Data Warehousing in Defense Environments
What Is Defense Data Warehousing and Why Does It Matter?
Defense data warehousing is a specialized system designed to manage the massive volumes of information generated by military operations worldwide. Unlike commercial data warehouses, defense systems must handle classified data, enable secure sharing across domains, and maintain around-the-clock operational readiness.
In simple terms, these warehouses act as central data hubs where information from sources such as satellites, sensors, logistics networks, and intelligence databases is securely stored and organized. Built on cloud platforms such as AWS GovCloud, they allow analysts, commanders, and decision-makers to access real-time insights on everything from troop readiness to tactical intelligence.
By moving from older, isolated systems to modern, cloud-based architectures, defense organizations can finally eliminate data silos that block collaboration. This integrated approach ensures that critical intelligence flows seamlessly across branches, commands, and even allied nations—helping improve coordination, speed, and overall mission success.
How Does Data Architecture Support DoD Mission Success?
Data architecture in defense contexts refers to the comprehensive framework of systems, policies, standards, and governance structures that govern how data is collected, classified, stored, secured, and used across the defense enterprise. The Defense Information Systems Agency (DISA) emphasizes strengthening data architecture and governance as a key line of effort in its 2025-2027 strategy, recognizing that robust architectural foundations are essential for maintaining technological superiority.
Effective DoD data architecture addresses several critical imperatives:
Interoperability and Data Sharing
Modern cloud architectures support federated data fabric approaches where security data can be centralized across domains while maintaining fine-grained access control. This enables the vision of data remaining at its origin while becoming discoverable and accessible to authorized users across the enterprise.
Real-Time Intelligence Processing
Advanced streaming technologies handle the high-velocity dataflows that military operations demand, ensuring that time-sensitive intelligence reaches decision-makers without delay. This capability is particularly crucial in contested environments where information superiority directly impacts mission outcomes.
Zero Trust Security Integration
The DoD Zero Trust Strategy mandates a cybersecurity framework where no user, network, or system is inherently trusted. The increasing adoption of zero-trust architectures with continuous authentication and least privilege access enables more fluid and robust cross-domain data sharing, a critical requirement for modern joint operations and coalition warfare.
AI-Ready Infrastructure
Organizations are enhancing data security, improving data quality practices, and updating data governance frameworks to address GenAI-specific demands, ensuring that defense data architectures can support artificial intelligence and machine learning initiatives that enhance warfighting capabilities.
What Are the Benefits of Modernizing DoD Data Infrastructure?
The strategic advantages of advanced data warehousing and architecture in defense operations extend across operational, tactical, and strategic levels:
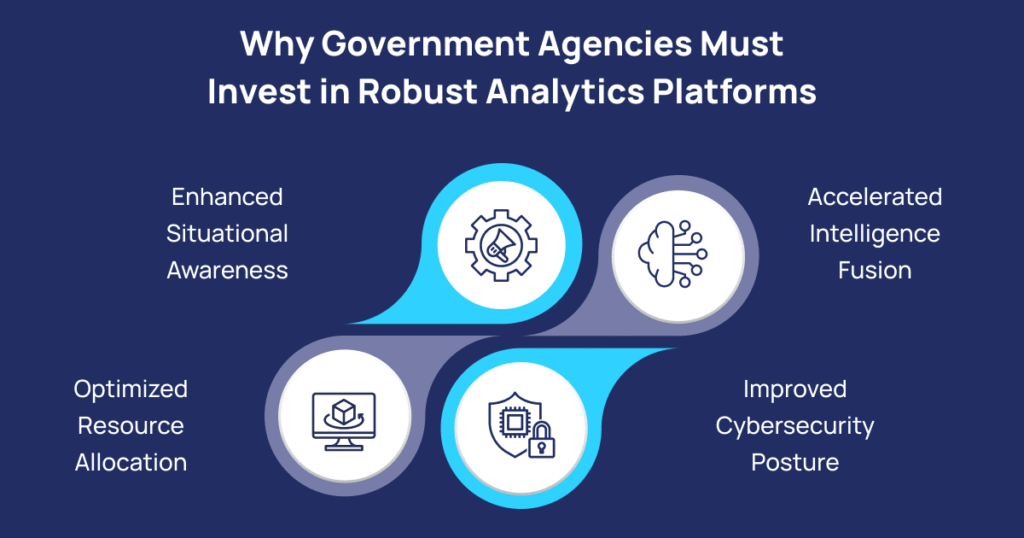
Enhanced Situational Awareness
Real-time access to integrated data from multiple intelligence sources provides commanders with comprehensive operational pictures, enabling faster, more informed decisions in dynamic threat environments. This capability transforms how military leaders assess situations, allocate resources, and respond to emerging threats.
Optimized Resource Allocation
Advanced analytics platforms built on modern data warehouses identify inefficiencies, redundancies, and optimization opportunities across logistics, personnel, and equipment management systems. Treating data as a strategic asset enables defense organizations to gain full value from DoD capabilities and investments, ensuring optimal use of taxpayer resources.
Accelerated Intelligence Fusion
Federated data fabrics leveraging open data standards and advanced analytics platforms like Open DAGIR, Advana, Army Advantage, and Navy Jupiter enable data interoperability across diverse defense environments. These systems allow intelligence professionals to correlate information from disparate sources rapidly, identifying patterns and threats that might otherwise remain hidden.
Improved Cybersecurity Posture
The DoD Zero Trust Strategy incorporates principles through granular access controls, encryption, continuous monitoring, and data-centric security measures that protect sensitive information throughout its lifecycle. Modern data architectures implement these zero-trust principles to achieve enterprise resilience against increasingly sophisticated cyber threats.
Coalition Collaboration: Effective data architecture facilitates information sharing with allied partners and coalition forces while maintaining appropriate security boundaries. This capability is essential for multinational operations where shared intelligence and coordinated responses determine mission success.
What Technologies Are Shaping the Future of Defense Data Solutions?
The landscape of defense data management continues to evolve rapidly, driven by technological innovation and emerging operational requirements:
Data Lakehouse Architectures
Data lakehouses combine the capabilities of data lakes and data warehouses, simplifying data architecture with unified storage and processing of structured, unstructured, and semi-structured data. This hybrid approach provides the flexibility to store raw data from diverse sources while supporting the performance requirements of advanced analytics and business intelligence applications.
Artificial Intelligence Integration
GenAI lives on unstructured data—text, images, videos, audios—as the most abundant source for generating new insights. Defense organizations are developing specialized data architectures that can effectively manage and govern unstructured data to support AI-driven intelligence analysis, predictive maintenance, and autonomous systems.
Edge Computing for Tactical Operations
Hybrid cloud architectures provide mission-critical functions to soldiers in contested environments through edge computing solutions that enable tactical data fabric across legacy enterprises and tactical networks. AWS Modular Data Centers allow the DoD to deploy self-contained data centers with built-in AWS infrastructure to locations with limited infrastructure, ensuring that warfighters maintain data access even when connections to centralized systems are degraded or unavailable.
Data Mesh Principles
Data mesh emphasizes decentralization and assigns ownership of data to individual domains within an organization, a concept that aligns well with the decentralized nature of military operations, where different commands and agencies maintain specialized data assets.
How Can Organizations Implement Effective DoD Data Solutions?
Successful implementation of modern data solutions in defense environments requires careful attention to several critical factors:
Governance and Compliance
DISA emphasizes the importance of data governance and operationalizing defense cyber data and business data as foundational elements. Organizations must establish clear policies, standards, and oversight mechanisms that ensure data quality, security, and compliance with regulatory requirements, including CMMC, ITAR, and classification protocols.
Agile Development Approaches
Adopting agile approaches to application and system development allows for rapid prototyping, testing, and deployment of software features, enabling defense organizations to adapt quickly to changing requirements and emerging threats. This flexibility accelerates capability delivery and enhances operational effectiveness.
Workforce Development
Fostering a data-centric culture and cultivating a data-driven workforce are essential for maximizing the value of data infrastructure investments. Organizations must invest in training programs that develop data literacy across all levels, from analysts to senior leaders.
Continuous Modernization
Legacy system integration and modernization present ongoing challenges. Successful organizations implement phased migration strategies that gradually transition from outdated infrastructure to modern cloud-based, data-centric architectures while maintaining operational continuity.
Partnership and Collaboration
Leveraging commercial innovation and partnering with industry leaders in data architecture, cloud computing, and cybersecurity accelerates capability development and ensures access to cutting-edge technologies. These partnerships bring specialized expertise and proven solutions to complex defense data challenges.
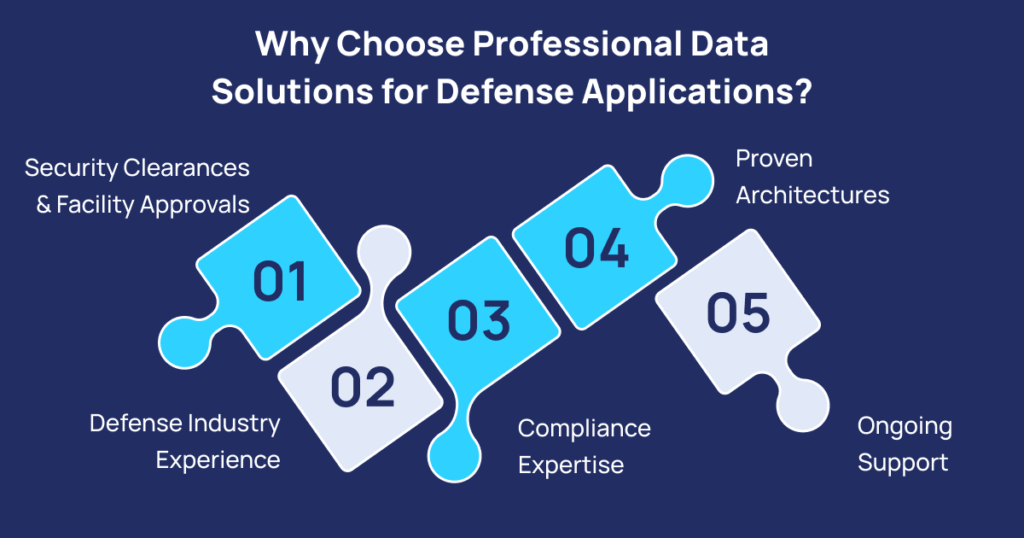
Why Choose Professional Data Solutions for Defense Applications?
The unique requirements of defense data management, including classification levels, cross-domain solutions, zero-trust security, and mission-critical reliability, demand specialized expertise that goes beyond standard enterprise data solutions. Professional services providers with a deep understanding of defense operations, security requirements, and compliance frameworks deliver solutions that meet both technical specifications and operational needs.
Organizations specializing in DoD data solutions bring:
- Security Clearances and Facility Approvals:Teams with appropriate clearances can work directly with classified data and systems
- Defense Industry Experience: Understanding of military operations, doctrine, and organizational structures
- Compliance Expertise: Knowledge of CMMC, FedRAMP, NIST frameworks, and classification requirements
- Proven Architectures: Reference implementations and best practices specific to defense applications
- Ongoing Support: Continuous monitoring, maintenance, and enhancement of data systems to maintain operational readiness
How Do Data Lakes Support Defense Analytics?
Modern defense operations generate unprecedented volumes of raw data from sensors, systems, and operations worldwide. Data lakes provide the scalable storage foundation necessary to capture this information in its native format without requiring upfront transformation or schema definition. This flexibility is particularly valuable for defense applications where new data sources frequently emerge and analytical requirements evolve rapidly.
Data lake governance ensures that while data remains accessible for analytics and AI applications, appropriate access controls, lineage tracking, and quality management practices maintain data integrity and security. Combined with advanced analytics tools, data lakes enable data scientists and intelligence analysts to explore vast datasets, identify patterns, and develop predictive models that enhance situational awareness and decision-making.
What Role Does Big Data Analytics Play in Defense Operations?
Big data analytics platforms transform raw information into actionable intelligence by processing vast quantities of structured and unstructured data at scale. These capabilities support critical defense functions, including:
- Threat Detection and Analysis:Identifying patterns in cyber activity, communications, and behavior that indicate potential threats
- Predictive Maintenance: Analyzing equipment sensor data to predict failures before they occur, improving readiness and reducing costs
- Logistics Optimization: Streamlining supply chains and resource distribution to ensure materials reach the right place at the right time
- Intelligence Fusion: Correlating information from multiple sources to develop comprehensive threat assessments
- Mission Planning: Analyzing terrain, weather, enemy capabilities, and other factors to optimize operational plans
Conclusion: Taking the Next Step in Defense Data Transformation
The need for modern data solutions in defense has never been more urgent. As global threats evolve and operations move faster, the ability to quickly collect, connect, and understand data has become a true game-changer. Defense organizations that invest in strong data warehousing, smart architecture, and solid governance gain a clear edge in today’s data-driven battlefield.
Whether your organization is just starting its data modernization journey or looking to strengthen existing systems, working with experienced experts who understand both the technology and defense mission goals is essential. From planning and design to deployment, optimization, and long-term support, the right partner can help turn your data challenges into powerful insights — transforming data from a complex burden into a valuable strategic advantage.
Ready to Modernize Your Defense Data Infrastructure?
PiTech’s comprehensive data solutions are specifically designed for government organizations and defense contractors seeking to build robust big data platforms, including data lakes, data lake governance, and advanced analytics capabilities. We support data science initiatives, AI/ML development, and mission-critical analytics across classified and unclassified environments.
Our team brings deep expertise in defense data architecture, cloud migrations, data warehousing, and analytics platform development. We understand the unique challenges of working with sensitive defense data and the stringent security, compliance, and reliability requirements that defense missions demand.
Key Takeaways
- Three pillars of DoD data success: Centralized repositories, robust security frameworks, and scalable architecture enable real-time intelligence for mission-critical decisions.
- Zero Trust Security is mandatory:Continuous authentication and least privilege access enable secure cross-domain data sharing across joint and coalition operations.
- Cloud platforms eliminate data silos:Modern architectures like AWS GovCloud ensure seamless intelligence flow across military branches, commands, and allied nations.
- Emerging technologies drive capabilities:Data lakehouses, AI/ML, edge computing, and data mesh principles support modern defense operations in contested environments.Data lakehouses, AI/ML, edge computing, and data mesh principles support modern defense operations in contested environments.
- Intelligence fusion accelerates response: Federated platforms (Open DAGIR, Advana, Army Advantage, Navy Jupiter) rapidly correlate disparate sources to identify threats.
- Implementation requires a holistic approach:Success demands governance compliance (CMMC, FedRAMP, NIST), agile development, workforce training, and specialized defense expertise.
- Data transforms into strategic advantage: Enhanced awareness, optimized resources, predictive maintenance, and improved cybersecurity turn data challenges into operational superiority.
Frequently Asked Questions (FAQs)
Why is modern data architecture critical for the Department of Defense?
Modern data architecture enables the DoD to unify data from multiple commands, systems, and intelligence sources. It eliminates silos, supports real-time decision-making, and ensures that mission-critical insights are available securely and instantly across operations.
How does the Zero Trust framework enhance defense data security?
The Zero Trust model operates on the principle of “never trust, always verify.” It enforces continuous authentication, least privilege access, and constant monitoring — ensuring that classified defense data remains protected from both external and insider threats.
What advantages do data lakehouse architectures bring to defense organizations?
Data lakehouses combine the scalability of data lakes with the structure of data warehouses, allowing the DoD to store and analyze both structured and unstructured data. This hybrid model improves intelligence processing, mission planning, and predictive analytics.
How does AI integration improve defense data analytics and operational efficiency?
AI enhances data-driven capabilities across the defense ecosystem by automating intelligence fusion, detecting anomalies, and predicting maintenance needs. It empowers commanders to act faster, with more precision and confidence in complex environments.
What steps can defense agencies take to modernize their data infrastructure effectively?
Agencies should begin by strengthening data governance and compliance frameworks, adopting cloud-native and Zero Trust architectures, training personnel in data literacy, and partnering with experienced providers like PiTech to ensure secure, scalable modernization.